Retirement Insights
Cybersecurity Practices Every Retirement Plan Sponsor Should Know
October 14, 2025
Unwavering confidence. That’s the feeling employers should have about their retirement plan recordkeeper’s data protection policies and practices. With breaches making headlines almost daily, many organizations and individuals have grown numb to the frequency of cybersecurity incidents. But behind the scenes, threat actors are quietly accumulating credentials, using each breach as a stepping stone to gain broader and deeper access to both structured and unstructured data.
Your organization cannot afford such risks and the resulting liabilities. Cybersecurity is a prime concern for you — and it must be for your retirement plan’s recordkeeper.
The Explosive Growth of Cybercrime
Cybercrime is evolving and increasing at an unprecedented pace, with ransomware, phishing and data breaches affecting organizations of every size and sector. On average, more than 2,328 cyberattacks occur daily, totaling 850,000 annually. The financial toll is staggering — cybercrime damages are projected to reach $10.5 trillion annually by the end of 2025, making it more than any of the world’s economies except for the two largest (U.S. and China).*
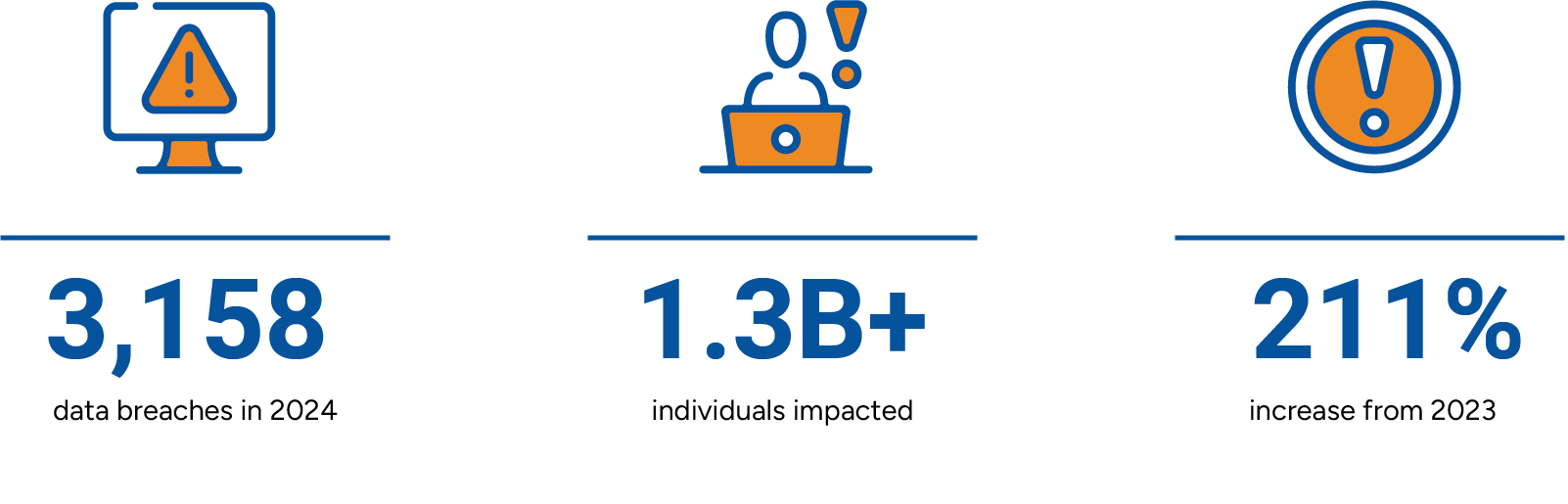
In 2024, the Identity Theft Resource Center reported 3,158 data compromises in the U.S. alone, impacting more than 1.3 billion individuals — a 211% increase year-over-year. This surge highlights the growing scale and sophistication of cyber threats, reinforcing the urgent need for proactive cybersecurity strategies.
Your cybersecurity should address these growing cyberthreats in particular:
- Business email compromise, social engineering, network intrusions, and ransomware incidents. The ransomware ecosystem has evolved to not only infiltrate and lock down, but also exfiltrate data as criminals leverage AI for faster, targeted and more streamlined attacks.
- Dependence on third- and fourth-party vendors, whose systems often serve as indirect entry points, making it easier for attackers to exploit weak links and gain access to sensitive data.
- Overreliance on AI-driven tools, which can create blind spots, especially if organizations fail to understand how decisions are made or overlook the need for human oversight.
The threat landscape is shifting rapidly, and organizations must adapt by strengthening identity controls, enhancing email security, and investing in AI-driven defense strategies to stay ahead.
Implement Best Practices for Cybersecurity
Retirement plan recordkeepers are entrusted with safeguarding sensitive client data. This responsibility extends beyond technology — it requires a proactive, strategic approach to cybersecurity.
Be sure to integrate the industry standard of “people, technology, and process” into your approach In other words, reinforcing persistent training across all organizational levels is essential to the cybersecurity of retirement plans because it ensures that every stakeholder, from leadership to frontline staff, is equipped to recognize and respond to evolving threats. This holistic approach builds a resilient defense posture by aligning human behavior, technological safeguards, and procedural rigor to protect sensitive participant data and plan assets.
The best practices outlined by the U.S. Department of Labor’s Employee Benefits Security Administration (EBSA) are a critical part of this holistic approach:
- Establish a formal, well-documented cybersecurity program.
- Conduct prudent annual risk assessments.
- Engage a reliable third party for annual audits of security controls.
- Clearly define and assign roles and responsibilities for information security.
- Implement strong access control procedures.
- Ensure cloud-based and third-party-managed data and assets undergo security reviews and independent assessments.
- Conduct periodic cybersecurity awareness training.
- Implement and manage a secure system development life cycle program.
- Develop an effective business resiliency program that addresses business continuity, disaster recovery and incident response.
- Encrypt sensitive data, both stored and in transit.
- Implement strong technical controls aligned with industry best practices.
- Document and respond appropriately to past cybersecurity incidents.
These best practices are integral to the cybersecurity strategy at USI Consulting Group (USICG). Our clients trust and place their confidence in us, and we take that responsibility seriously.
Preventative Measures 24/7
To safeguard client data and assets, we’ve made substantial investments in technology, personnel and infrastructure. These are reinforced by rigorous daily practices, policies and procedures designed to uphold the highest standards of cybersecurity.
Security is built into our routine. System access and data management are two key focus areas.
- Access control: We prevent unauthorized changes to corporate systems and enforce restricted network access via secure VPN, complex passwords and multifactor authentication.
- Data protection: Client data is encrypted, isolated and accessible only to those with privileged clearance. All data transfers with our partners use secure file transfer protocol, ensuring encryption meets the highest industry standards.
Don’t Overlook Cyber Insurance
While strong recordkeeping cybersecurity practices are essential, they’re only part of the equation. To fully protect your organization from the financial impact of cyber incidents, it’s equally important to evaluate your cyber insurance strategy.
Organizations should look to align crime and cyber policies coverage, and consider whether insurers will provide coverage under both policies for the same insured, which policy pays first, and how retentions or deductibles apply to larger losses.
Through our parent company USI Insurance Services, we have cyber risk and insurance experts who specialize in identifying and prioritizing risk to help clients understand their unique cyber exposures. We work with clients to reduce those exposures and secure adequate coverage by reviewing existing policies and benchmarking limits and retention, thereby identifying weaknesses in their current insurance program structure.
How We Can Help
USI Consulting Group is a long-trusted partner committed to protecting client data and assets through robust cybersecurity measures. Whether you're looking to strengthen your organization’s cybersecurity posture or evaluate the security protocols of your current provider, we're here to help.
Reach out to your local representative, visit our Contact Us page, or reach out to us at information@usicg.com.
*BD Emerson, Cybercrime Statistics 2025.
This information is provided solely for educational purposes and is not to be construed as investment, legal or tax advice. Prior to acting on this information, we recommend that you seek independent advice specific to your situation from a qualified investment/legal/tax professional.
INSIGHTS BY TOPIC
Not receiving our newsletter?
Stay up to date with retirement plan updates and insights by subscribing to our email list.
